What Is the SIG Questionnaire? Types, Risk Domains, and How to Respond
Article written by
Kaushik Natarajan

INSIDE THE ARTICLE
SHARE THIS ARTICLE
Summary
The SIG Questionnaire is the most widely used third-party vendor security assessment in enterprise procurement. This guide breaks down what the SIG is, the difference between SIG Lite and SIG Core, all 21 risk domains in the 2026 edition, a step-by-step response process, common mistakes to avoid, and how AI is transforming the way vendor teams handle SIG responses.
The SIG questionnaire is the most widely used vendor security assessment in enterprise procurement, integrated into 30+ TPRM platforms and with over 100,000 exchanged every year. And with 59–60% of data breaches linked to third-party vendor access, per Ponemon Institute and Verizon's 2024 DBIR, buyers are not slowing down on due diligence. This guide covers what the SIG is, how SIG Lite (128 questions) and SIG Core (627 questions) differ, all 21 risk domains, a step-by-step response process, and how AI is cutting SIG Core response time from days to hours. Let's dive in.
What is SIG?
The SIG Questionnaire is a comprehensive IT security assessment tool used by organizations to evaluate the security and risk controls of third-party vendors. It creates a uniform benchmark that both assessors and vendors can use reliably, replacing the inconsistency of custom, one-off security questionnaires.
Still answering SIG questionnaires manually?
SparrowGenie auto-fills verified responses from your approved knowledge base.
How the SIG Differs from SOC 2, ISO 27001, and CAIQ
Before diving into how to respond, let us clear up a common source of confusion. The SIG is not a certification. It is not an audit. It is a self-assessment questionnaire that gathers detailed information about your security and compliance posture.
Here is how it sits alongside other instruments in the vendor risk management ecosystem:
Instrument | Type | Purpose | Who Performs It |
|---|---|---|---|
SIG Questionnaire | Self-assessment questionnaire | Gather vendor security information across 21 risk domains | Vendor self-reports |
SOC 2 Report | Independent audit attestation | Verify operational security controls over time | Licensed CPA or auditor |
ISO 27001 | Certification | Confirm a working ISMS is in place | Accredited certification body |
CAIQ | Cloud-specific questionnaire | Assess cloud service providers against CSA CCM | Vendor self-reports |
The key insight: a completed SIG acts as evidence of due diligence, while SOC 2 or ISO 27001 certification independently verifies the controls you describe. Many enterprise buyers request the SIG as a prerequisite and then accept your SOC 2 report as supporting evidence within your SIG response. They work together, not as substitutes.
SIG Questionnaire Types: Lite, Core, and Custom
The SIG is not a one-size-fits-all document. Shared Assessments offers multiple versions calibrated to different vendor risk levels. Understanding which version you are completing is the first step in any SIG response.
Version | Questions (2025) | Best Used For |
|---|---|---|
SIG Lite | ~128 questions | Preliminary screening, low-risk or peripheral vendors |
SIG Core | ~627 questions | High-risk vendors handling sensitive or regulated data |
SIG Detail (Full) | 1,936 questions | The deepest possible assessment for critical engagements |
Custom/Scoped | Varies | Tailored to specific domains, industries, or regulations |
SIG Lite
SIG Lite is designed for early-stage vendor evaluation or for vendors handling non-sensitive data. With around 128 questions, it provides a high-level overview of key security controls covering general governance, basic data protection, and preliminary compliance metrics. It is commonly used during the RFP prequalification stage to filter out unsuitable vendors before a deeper review begins.
SIG Core
SIG Core is the comprehensive version required for critical vendors with access to sensitive data, infrastructure, or regulated systems. At 627 questions across 21 risk domains, it covers advanced controls: identity access management, threat detection, incident response, subcontractor oversight, and physical security. For enterprise SaaS vendors, a fast and accurate SIG Core response can materially accelerate deal closure.
Custom/Scoped SIG
Enterprise buyers may combine sections from SIG Core and SIG Lite, add up to 100 proprietary questions, and tailor the scope to industry-specific requirements such as FedRAMP, PCI-DSS, or HITRUST. Custom SIGs demand even greater cross-functional coordination from the responding vendor team.
The 21 SIG Risk Domains (2025 Edition)
The SIG questionnaire covers 21 distinct risk domains organized under four major control area categories. This structure lets buyers assess vendors consistently across an entire ecosystem of security and compliance concerns.
Governance and Risk Management
- Compliance Management: Adherence to regulatory obligations and internal policy frameworks
- Enterprise Risk Management: Organizational risk governance, risk appetite, and escalation processes
- ESG: Sustainability and ethical governance practices
- Human Resources Security: Background checks, onboarding/offboarding security, personnel controls
- Information Assurance: Policies, standards, and audit processes for information security management
- Nth Party Management: Risk oversight of your vendors' own vendors (sub-processors, fourth parties)
- Privacy Management: Data subject rights, privacy notices, GDPR/CCPA compliance
- Supply Chain Risk Management: Cybersecurity across the full supply chain lifecycle
Information Protection
- Access Control: Role-based access, MFA, account lifecycle management
- Application Management: SDLC security, code review, vulnerability management
- Cloud Services: Cloud security architecture, shared responsibility model compliance
- Endpoint Security: Device management, patching, anti-malware, mobile security
- Network Security: Firewalls, segmentation, intrusion detection/prevention systems
- Physical and Environmental Security: Building access, surveillance, environmental safeguards
- Server Security: Server hardening, patch management, host-based controls
- Artificial Intelligence (AI): AI risk governance, model reliability, bias, and transparency controls
IT Operations and Business Resilience
- Asset and Information Management: Inventory, classification, and lifecycle management of data and assets
- IT Operations Management: Change management, ITIL practices, operational procedures
- Operational Resilience: Business continuity, disaster recovery, failover testing
Security Incident and Threat Management
- Cybersecurity Incident Management: Incident detection, response procedures, breach notification timelines
- Threat Management: Threat intelligence, vulnerability scanning, penetration testing programs
Framework Mappings: One Response, Multiple Compliance Proofs
One of the SIG's most powerful features is its built-in alignment to 31 major regulatory and security frameworks in the 2025 Content Library. Key mappings include:
- ISO/IEC 27001:2022 and ISO/IEC 27002:2022
- NIST SP 800-53 Rev. 5 and NIST CSF 2.0
- GDPR, HIPAA, PCI-DSS, CCPA
- EU DORA (Digital Operational Resilience Act), new in 2025
- NIS2
- Cloud Security Alliance Cloud Controls Matrix (CCM)
What this really means is that a single well-completed SIG response can simultaneously evidence compliance across multiple frameworks, dramatically reducing vendor assessment overhead. Instead of filling out five different questionnaires for five different buyers, you build one authoritative response and reuse it.
How many hours did your last SIG Core response take?
SparrowGenie cuts that to under 3. No fluff. Just verified, confidence-scored answers from your own documentation.
Who Typically Responds to a SIG Questionnaire?
A SIG questionnaire is inherently cross-functional. No single team can complete it alone because the domains span IT, legal, compliance, HR, and operations.
- Security and IT Teams: Own technical domains including network architecture, endpoint protection, access control, vulnerability management, cloud infrastructure, encryption, and disaster recovery
- Compliance, Risk, and Legal Teams: Provide governance documentation, certifications (SOC 2, ISO 27001, HIPAA), privacy policies, breach notification protocols, and third-party oversight records
- Proposal and Pre-Sales Teams: Coordinate timelines, bridge technical SMEs and sales, maintain tone consistency, and format the final deliverable
- Sales and Account Executives: Drive urgency, provide context on buyer priorities, and ensure the response narrative aligns with the sales engagement
Manually completing a SIG Core typically takes 15 to 30 hours of internal effort, involving multiple rounds of SME input and review cycles. That makes efficiency and process the most critical factors in SIG response management.
How to Respond to a SIG Questionnaire: A Step-by-Step Process
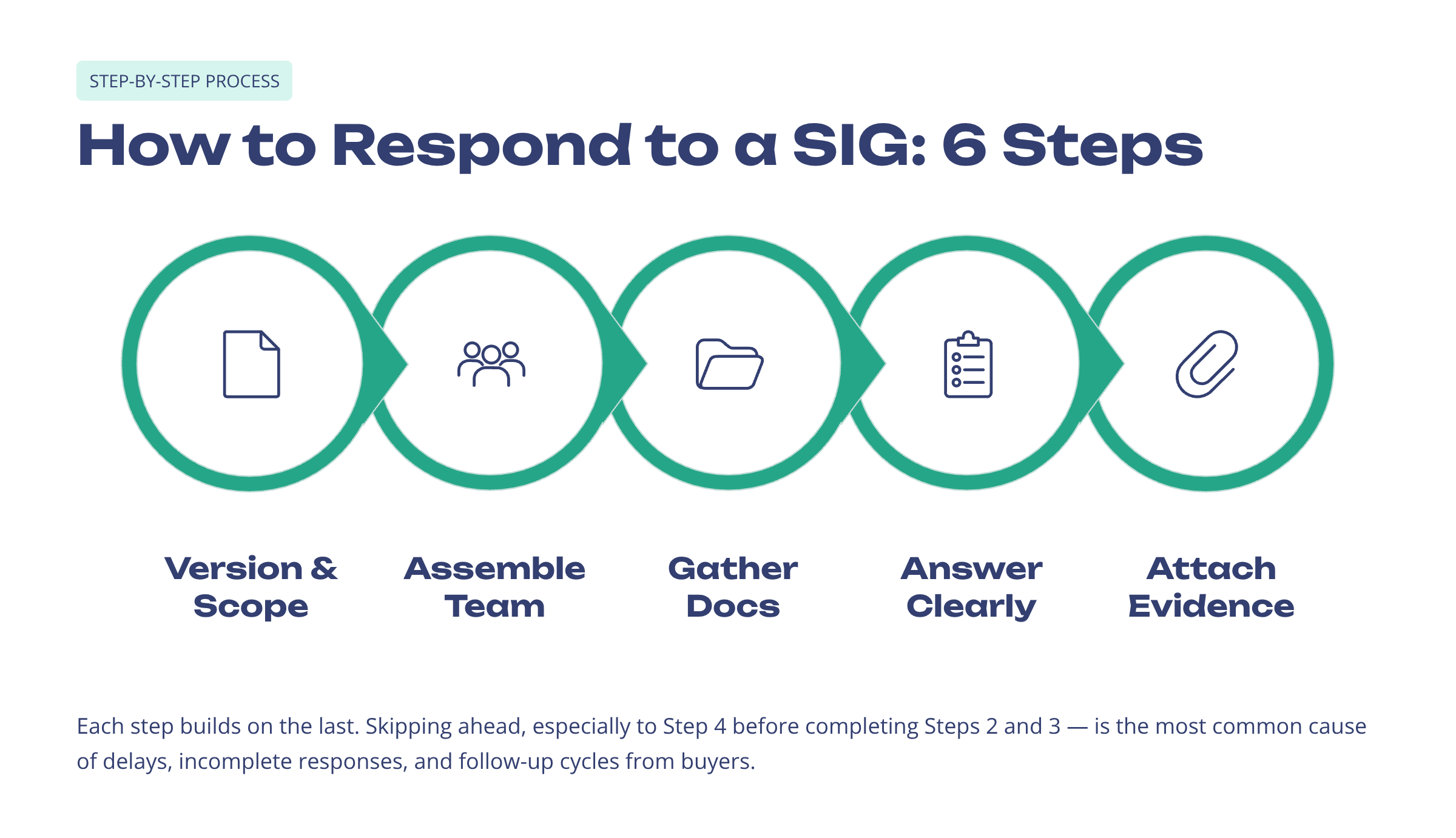
Now for the part you actually came here for. Let us break down the SIG response process into six actionable steps.
Step 1: Understand the Version and Scope
Before writing a single answer, identify which version of the SIG has been sent: SIG Lite, SIG Core, or a custom scoped version. Review the number of questions, the domains included, and whether any industry-specific modules have been added. Check the submission deadline and plan backwards from it.
Step 2: Assemble Your Cross-Functional Team
Assign section ownership early, matching each of the 21 domains to the appropriate internal subject matter expert (SME):
- Access Control, Network Security, Endpoint Security → IT/Security Team
- Compliance Management, Privacy Management → Legal/Compliance Team
- HR Security → HR or People Operations
- Cloud Services → Cloud or DevOps Team
Pro Tip: Waiting to identify owners at the last minute is the single most common cause of delays and incomplete responses. Map your SMEs to domains before your first SIG arrives, not after.
Step 3: Gather Supporting Documentation
Buyers rarely accept verbal attestations alone. Collect and index the following evidence before answering:
- Security certifications: SOC 2 reports (Type I/II), ISO 27001 certificate, PCI-DSS attestation
- Policies: Information Security Policy, Data Retention Policy, Incident Response Plan, BCP/DR Plan
- Technical artifacts: Network diagrams, data flow diagrams, penetration test results, vulnerability scan summaries
- HR documentation: Security training completion records, background check policies
- Third-party management: Vendor assessment procedures, sub-processor lists
If your organization has already completed a CAIQ or undergone a SOC 2 audit, use those responses and evidence packages as a reference. Many questions overlap significantly, which saves hours of duplicate work.
Step 4: Answer Questions Accurately and Concisely
This is where most vendors either win trust or lose it. Apply these response principles for every question:
- Be truthful: Answer from your actual security and compliance program. Do not fabricate controls you do not have. If a control is on your roadmap, state the timeline honestly.
- Be concise: Answer the specific question asked. Avoid over-sharing information that was not requested.
- Provide context: For complex controls, briefly explain how the control works, not just that it exists.
- Watch for repeated questions: SIG reviewers intentionally ask the same question in different ways to test consistency. Ensure your answers align across all domains.
- Use industry-standard language: Reference concepts like least privilege, zero trust, MFA, or segregation of duties to signal maturity.
For questions where your organization does not yet have a control: acknowledge the gap, state any compensating controls, and provide an honest timeline for remediation. Procurement teams respect transparency far more than evasion.
Step 5: Attach Supporting Evidence
Wherever a question asks about certifications, policies, or procedures, attach the relevant documentation. Failing to provide evidence when requested is one of the most common causes of follow-up cycles and delayed approvals. Create a documentation checklist mapped to the SIG domains and ensure all attached documents are current versions. Expired certificates or outdated policies signal poor security hygiene.
Step 6: Review for Consistency Before Submission
Before submitting, conduct a full cross-domain review with both a technical reviewer and a compliance/legal reviewer:
- Check that terminology is consistent throughout (if you call your incident response process CSIRT in one section, use the same term everywhere)
- Verify that answers in one domain do not contradict answers in another
- Ensure all evidence attachments are linked to the correct questions
- Confirm the submission format matches the buyer's requirements (Excel, PDF, portal upload)
How many hours did your last SIG Core response take?
SparrowGenie cuts that to under 3. No fluff. Just verified, confidence-scored answers from your own documentation.
Best Practices for Efficient SIG Response Management
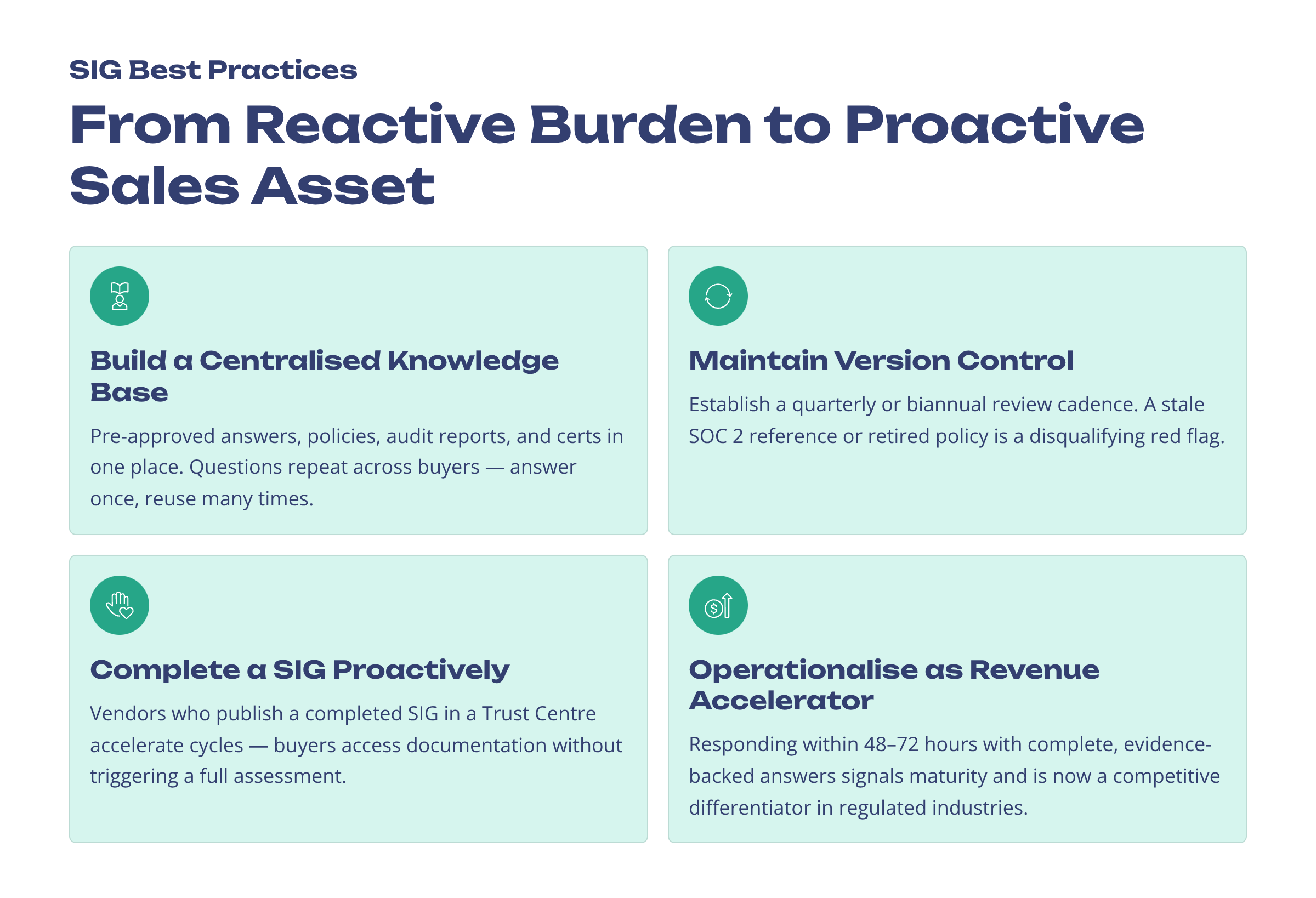
Build a Centralized Knowledge Base
The most impactful structural investment a vendor team can make is a centralized content library: a single source of truth containing pre-approved answers, security policies, audit reports, diagrams, and certification documents. Many questions repeat across SIG questionnaires from different buyers. Organizations with a well-maintained knowledge base can respond in a fraction of the time compared to those starting from scratch.
Maintain Version Control and Content Freshness
Security postures evolve: policies update, certifications renew, infrastructure changes. A stale answer referencing an expired SOC 2 report or a retired policy can be a disqualifying red flag. Establish a quarterly or biannual review cadence to audit your SIG content for accuracy.
Complete a SIG Proactively as a Self-Assessment
One of the most effective strategies is to complete a SIG questionnaire before any customer sends one. Vendors who proactively fill out the SIG and publish key artifacts in a Trust Center significantly accelerate sales cycles, as buyers can access security documentation without initiating a full assessment process. This transforms the SIG from a reactive compliance burden into a proactive sales enablement asset.
Operationalize SIG as a Revenue Accelerator
Research from Gartner indicates that 60% of organizations say delays in vendor security assessments are a key blocker in contract execution. Vendors that respond to SIG questionnaires within 48 to 72 hours, with complete and evidence-backed answers, signal organizational maturity and significantly reduce friction in the procurement cycle. For SaaS vendors in regulated industries, SIG response quality is now a competitive differentiator.
Common Mistakes to Avoid When Responding to a SIG
Even experienced teams trip up. Here are the seven most common SIG response mistakes and how to avoid them:
Mistake | Impact | How to Avoid |
|---|---|---|
Reusing outdated responses | Expired certifications or retired policies signal risk | Version-control your content library; audit quarterly |
Skipping SME input | Vague or technically incorrect answers | Assign domain owners at the start |
Inconsistent terminology | Confuses reviewers; reduces credibility | Use pre-approved, standardized language |
Ignoring evidence requests | Triggers follow-up cycles; delays approvals | Maintain a documentation checklist per domain |
Leaving questions blank | Signals incompleteness or non-compliance | Mark N/A with explanation if truly not applicable |
Rushing the final review | Contradictions and errors slip through | Build a multi-stakeholder approval workflow |
Treating SIG as formality | Misses the revenue impact of a strong response | Position SIG as a strategic sales tool |
How AI and Automation Are Changing SIG Responses
Let us talk about where this is all heading. Manual SIG responses are increasingly being replaced by AI-powered automation tools that dramatically reduce turnaround time. According to vendors in this space, AI can auto-answer 70 to 90 percent of SIG questions by matching them semantically to an organization's existing documentation and compliance evidence.
Key AI capabilities in modern SIG response tools include:
- Natural Language Understanding (NLU): Parses question intent rather than relying on keyword matching, handling rephrased or domain-shifted questions accurately
- Content Retrieval: Maps questions to the most relevant pre-approved answers, policies, and certifications from the knowledge base
- Confidence Scoring: Flags AI-generated answers by reliability, directing human reviewers to focus only on uncertain or high-risk responses
- Gap Detection: Automatically identifies incomplete or contradictory answers before submission
- Continuous Learning: Improves answer quality over time based on reviewer edits and approval history
With AI assistance, the 15 to 30 hour manual process for SIG Core can be reduced to under 3 hours. That is not an incremental improvement. That is a structural shift in how vendor security assessments get done.
Where SparrowGenie Fits: SparrowGenie's AI-native architecture was built specifically for high-stakes questionnaire and RFP response workflows. Its Knowledge Hub acts as the centralized content library that the SIG process demands, with a Train-Test-Improve loop that continuously strengthens answer quality. Confidence scoring on every AI-generated answer means your reviewers focus only on what needs human judgment, not on re-verifying every line. And with SOC 2 Type II compliance, zero data retention, and data isolation, your SIG response platform meets the same security standards your SIG answers describe.
How to Access the SIG Questionnaire
The SIG is not a free tool. Access requires either a Shared Assessments membership or a standalone corporate license, priced at approximately $6,500 per year. The license includes the SIG Manager (an Excel-based scoping and templating engine), the full SIG Content Library with all questions and framework mappings, a standardized Response Template for vendors, and user guides with supporting documentation.
For organizations that do not purchase a SIG license directly, many third-party risk management (TPRM) platforms are licensed SIG resellers that include SIG templates within their platform subscriptions.
Conclusion: Treat the SIG as a Sales Asset
The SIG questionnaire has become the central infrastructure of enterprise vendor risk management. For buyers, it provides a scalable, framework-aligned method for assessing hundreds of vendors consistently. For vendors, it is a critical gatekeeper in the enterprise sales process.
The most effective approach is to treat the SIG not as a reactive compliance requirement but as a proactive sales asset. That means building a centralized knowledge base, completing the SIG as a self-assessment before customers ask for it, and investing in AI-assisted tools to scale responses without scaling headcount.
Organizations that master the SIG response process are positioning themselves as enterprise-grade partners in an era where third-party risk scrutiny has never been higher. The question is not whether you will need to complete a SIG. It is whether you will be ready when the next one arrives.
Ready to Automate Your SIG Responses?
SparrowGenie helps enterprise teams respond to SIG questionnaires, security assessments, DDQs, and RFPs faster with AI-powered confidence scoring and a self-improving Knowledge Hub. See how it works.
Ready to see how AI can transform your RFP process?
Kaushik Natarajan is the Head of Solution Engineering at SurveySparrow with over a decade of experience in the CRM and customer experience industry. He has previously worked with companies such as Yellow.ai, Freshworks, Newgen Software, and CRMNEXT. Kaushik specializes in requirements gathering, solution architecture, and bridging the gap between technical capabilities and business objectives. His hands-on experience with CRM consulting and implementations gives him unique insight into what drives successful technology adoption.


